How Much Bandwidth Do Your IT Services Actually Use?
Nfdump displays the traffic among network devices and thereby allows seeing how much bandwidth is consumed by the single flows. This may be a useful information, but indeed, it is not very meaningful. Since Nfdump just lists the single flows between two ports (including the generated traffic), it is difficult to understand at a glance:
- To which service a flow belongs
- How many flows (and traffic) a certain service generates
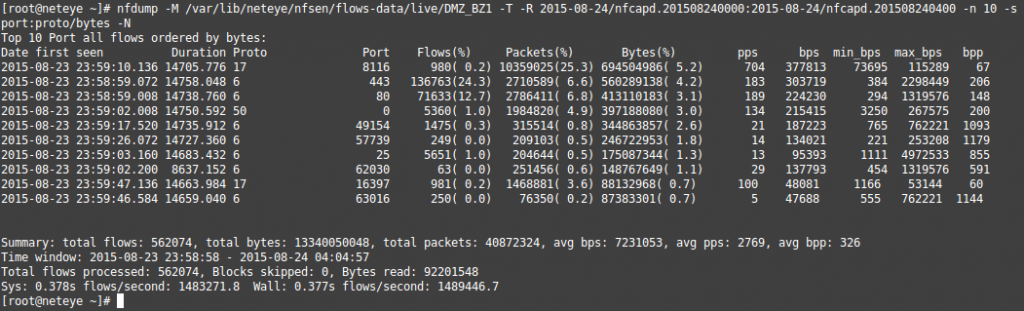
Nfdump just allows to display the traffic among network devices and thereby, seeing how much bandwidth is consumed by the single flows.
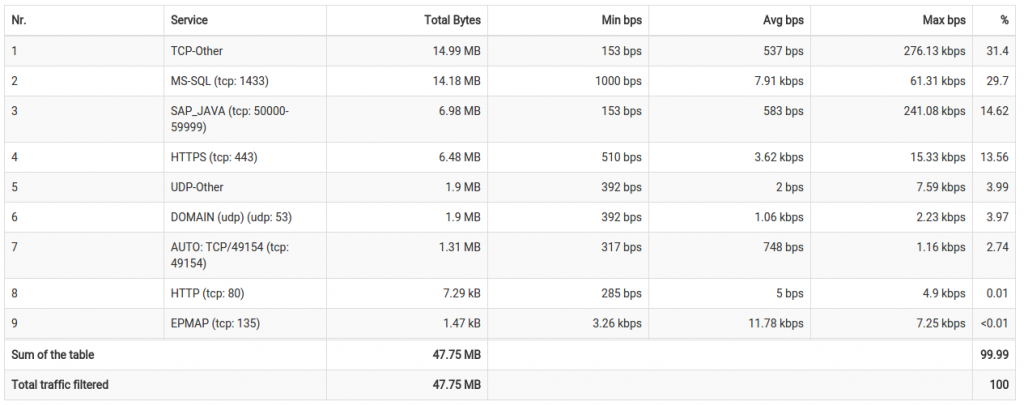
Actually, we want to know, which service generated most traffic during a certain period. To get this information, we have to associate the single flows to a certain service. How can we do this? – Based on the network ports we can identify, which flows belong to which service. Summarizing all flows, which belong to one service, we can see at a glance, how much bandwidth was consumed by the single services.
We integrated a new functionality to the NetEye Reporting to visualize the generated traffic by the different IT service. This functionality allows you, within the sections Top Flow Statistics and Top In/Out Flows, to classify the flows according to the network ports and to associate them to specific services (like HTTP, IMAP, SMTP and so on). Beside the default network services, you have the possibility to specify your own services and to associate specific ports to them.
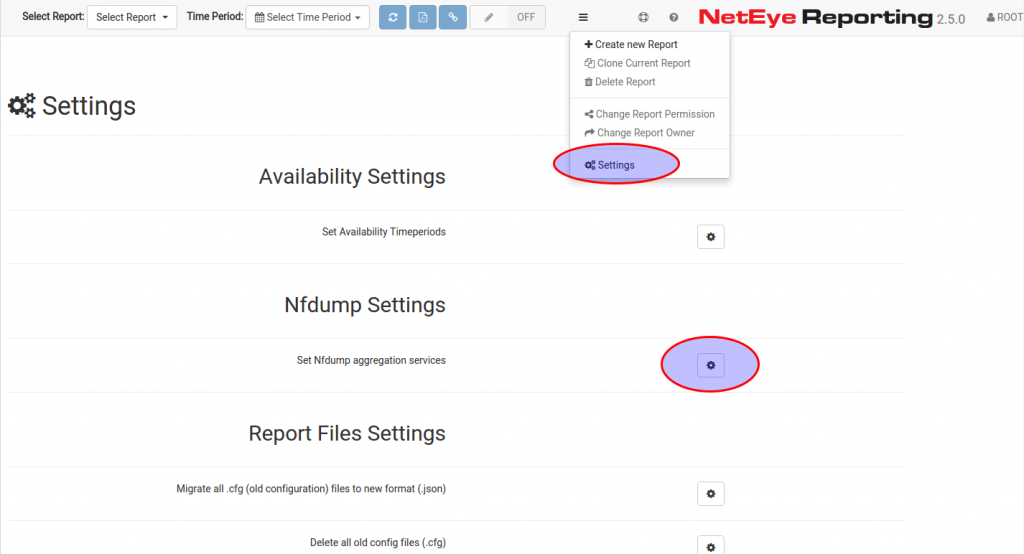
Example: In your network, the ERP system (exmpl.: SAP or Microsoft Dynamics) may use all TCP ports from 50000 to 59999 and therefore you want to associate all that flows to the ERP service. To do so, open the NetEye Reporting Settings from the main menu in the section Nfdump Settings, here you will find Set Nfdump aggregation services (see picture below).
The displayed dialog allows you to open an already created service-set or to create a new one, where you can specify the ports, which have to be associated to the new service. Additionally, you can also choose to clone an already created service-set by clicking on the “clone” button. Once you defined the service-set you can choose which one to use in your report (in the sections Top Flow Statistics and Top In/Out).
![Define Nfdump aggregations [2/2]](http://www.neteye-blog.com/wp-content/uploads/2015/08/Selection_080.png)






