A important part of Windows auditing is to track file and folder access on Windows file volumes. Out of the box, this part of auditing is not enabled on Windows operating systems. It’s necessary to enable file and folder auditing and then identify the files and folders that are to be audited. Once correctly configured, the server security logs will then contain information about attempts to access or otherwise manipulate the designated files and folders. It is important that file and folder auditing is only available for NTFS volumes!
Enabling File and Folder Auditing
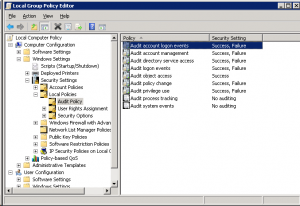
File and folder auditing is enabled and disabled by using Group Policys (for domains, sites and organizational units) or local security policys (for single servers). To enable file and folder auditing for a single server, select Start -> All Programs -> Administrative Tools -> Local Security Policy or type on the run command “gpedit.msc”. In the Local Security Policy tool, expand the Local Policies branch of the tree and select Audit Policy.
In the default no security settings for the audit policies are enabled. Remember, if we work in a domain environment the domain group policy with entry’s for security settings overwrite the entry’s on the local security policies settings!
Before we can audit file and folder access, we must enable the “Audit Object Access” setting in the machine’s or domain group policy. We can enable these types of auditing by double-click of the appropriate option in the Local Security Policy Settings console.Than we can implement a failure audit and/or a success audit for each event.
So how do you know whether to perform a success or a failure audit? Well, that’s really up to you. For logins and policy changes, I recommend auditing both success and failures. For example, a success audit of login actions would create an audit log entry every time someone logged in successfully. A failure audit of the same event would write an audit log entry every time someone entered a password incorrectly. Likewise, a success audit on policy changes would let you know that someone changed a security policy, while a failure audit would tell you that someone tried to change a security policy but didn’t actually manage to make the change happen.
When it comes to auditing object access, I recommend also enabling success and failure audits. Just because success and failure audits are enabled for object access, though, it doesn’t mean that you actually have to use them. Every object that you audit access for has an entire range of audit options. Enabling success and failure audits simply make these options available to you.
Once file and folder access auditing has been enabled the next step is to configure which files and folders are to be audited. As with permissions, auditing settings are inherited unless otherwise specified. By default, configuring auditing on a folder will result in access to all child subfolders and files also being audited. Just as with inherited permissions, the inheritance of auditing settings can be tuned off for either all, or individual files and folders.
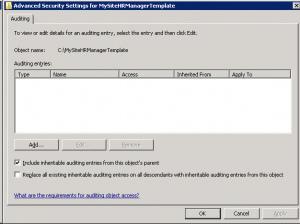
To configure auditing for a specific file or folder begin by right clicking on it in Windows Explorer and selecting Properties. In the properties dialog, select the Security tab and click on Advanced. In the Advanced Security Settings dialog select the Auditing tab. Auditing requires elevated privileges. If not already logged in as an administrator click the Continue button to elevate privileges for the current task. At this point, the Auditing dialog will display the Auditing entries list containing any users and groups for which auditing has been enabled as shown below:
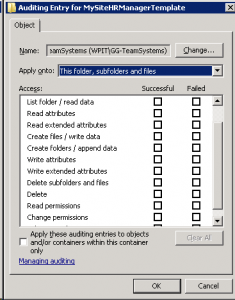
To add new users or groups whose access attempts to the select file or folder are to be audited click on the Add…’ button to access the Select User or Group dialog. Enter the names of groups or users to audit, or Everyone to audit access attempts by all users. Click on OK to display the Auditing Entries for dialog as illustrated below:
Use the drop down list to control whether the auditing setting is to be applied to the current file or folder, or whether it should propagate down to all children files and/or sub-folders. Finally, select which types of access are to be audited and, for each type, whether successful, failed or both kinds of attempt are to be audited. Once configured, click on OK to dismiss current dialog and then Apply the new auditing settings in the Auditing Entries dialog.
From this point on, access attempts on the selected file or folder by the specified users and groups of the types specified will be recorded in the server’s security logs.

Thanks for sharing this helpful post.
I also find a very informative PDF guide that provides step-wise instructions to enable auditing on file server and track every changes into real time : http://www.lepide.com/guide/enable-file-folder-access-auditing.pdf