Network Discovery and Asset Inventory: A Useful Comparison
Most of our customers know and use NeDi for network discovery and inventory, and GLPI for asset management.
These NetEye modules have two important results, if they are implemented and used in the best way:
- Having an active discovery tool to identify each device connected to the company network: from the main network devices to each connected MAC address
- Maintaining an accurate inventory, managing the asset life cycle (from purchase order to the disposal), and all their interrelationships.
Have you ever wondered how interesting it could be to compare data from these two databases?
With a Grafana dashboard you can do it very effectively and highlight, for example, which MAC addresses were detected in the discovery phase but were not present in the inventory database, and thus are potentially unauthorized!
How important is inventory and control of hardware assets?
The first of the 20 Critical Security Controls published by the Center for Internet Security (CIS) is the following:
CSC 1: Inventory and Control of Hardware Assets
Key Principle:
Actively manage (inventory, track, and correct) all hardware devices on the network so that only authorized devices are given access, and unauthorized and unmanaged devices are found and prevented from gaining access.
Main Points:
- Utilize an active discovery tool to identify devices connected to the organization’s network and update the hardware asset inventory.
- Maintain an accurate and up-to-date inventory of all technology assets with the potential to store or process information. This inventory shall include all hardware assets, whether connected to the organization’s network or not.
The Center for Internet Security (CIS) is a forward-thinking, nonprofit entity that harnesses the power of a global IT community to safeguard private and public organizations against cyber threat.
The proposed controls constitute a guideline on measures to implement data protection systems, and represent global best practice, as they are developed by a community of cybersecurity experts who work daily in the defense of systems and networks, and therefore have direct experience and contact with company operations.
The CIS controls are listed in order of priority and are designed to mitigate the most common attacks against networks and information systems of companies and institutions.
The AGID (Agenzia per l’Italia Digitale) based its 2017 directive on minimum protections for Public Administration, which in turn is based on CIS Controls V5 and V6.
Grafana dashboard
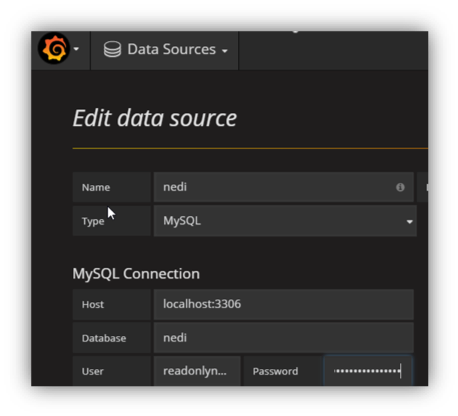
The NeDi and GLPI databases are managed on MySQL. Grafana ships with a built-in MySQL data source plugin that allows you to query and visualize data from a MySQL-compatible database.
To query a database from Grafana, the first step is to create a new Data Source as in the following example (for each connection to the NeDi DB and to the GLPI DB).
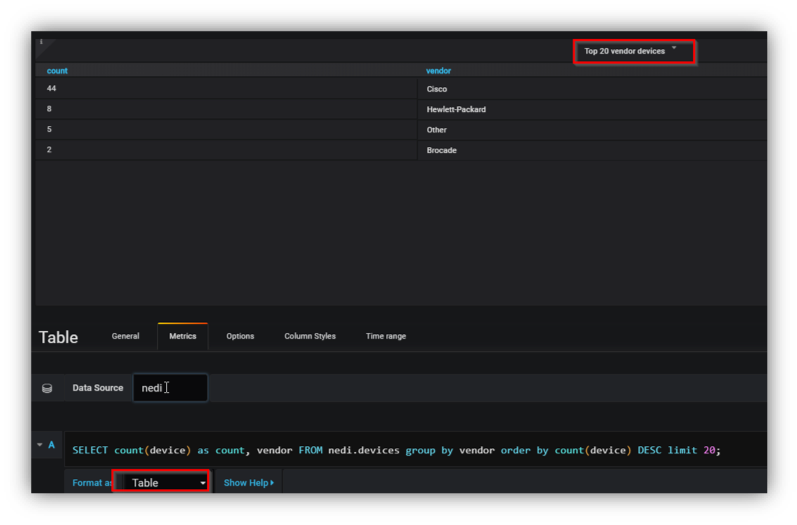
Then you can start building a new dashboard including statistics tables that show, for example, the Top 20 vendors’ devices found by NeDi like the following:
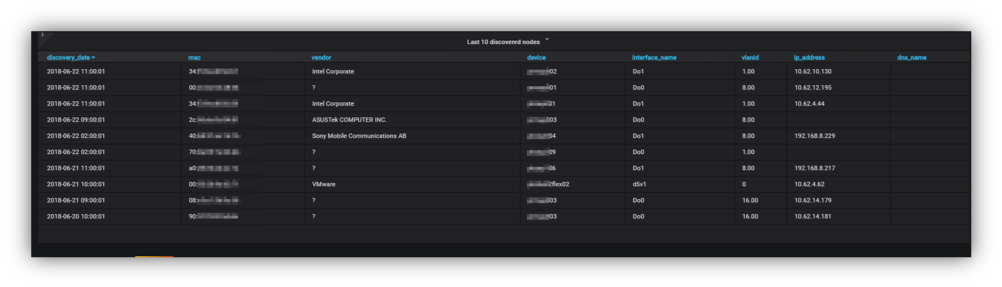
Thanks to NeDi it is possible to have very accurate information on the “status” of a MAC address not present in GLPI’s inventory DB. Within this information you can identify the device to which it’s connected, its network interface, the vlan, the respective IP address and, if present, the DNS name.
Thus you can create tables like the following to highlight the differences between the MAC addresses detected by NeDi and those present on GLPI (per switch, per vlan, or filtering any kind of information needed)
Conclusions
Thanks to dashboards like the one above, you can have a rather comprehensive view of unauthorized accesses, or better yet, of those accesses not known to the inventory system and that therefore must be verified.
The requirements are two: timely network discovery and an inventory system that is as up-to-date as possible.
This post originated from an idea with Paolo Pintossi of Cembre SpA. Thanks for his cooperation.
For more information about CIS Controls, please click here.