On our OpenShift cluster we use pulp3 as the repository manager.
One recent task we had to do was to add a certificate before we could expose the repository over TLS. Our IT department provided us with the certificate in .pfx format.
Following this guide for converting the certificate to a format usable by OpenShift, we first extracted the key from the .pfx file using openssl. Pulp Operator requires the certificate and the key to be stored in a secret and the key to be decrypted:
# openssl pkcs12 -nocerts -in ./pulp3.apps.rdopenshift.si.wp.lan_exp2028.pfx --out pulp3.apps.rdopenshift.si.wp.lan_exp2028.key
Next we wanted to extract the public certificate. Note that we include the full chain (-chain ) and extract only the client cert (-clcerts):
# openssl pkcs12 -clcerts -nokeys -chain -in ./pulp3.apps.rdopenshift.si.wp.lan_exp2028.pfx --out pulp3.apps.rdopenshift.si.wp.lan_exp2028.crt
If we use a custom CA, we can extract that too from the .pfx file:
# openssl pkcs12 -cacerts -nokeys -chain -in ./pulp3.apps.rdopenshift.si.wp.lan_exp2028.pfx --out pulp3.apps.rdopenshift.si.wp.lan_exp2028-ca.crt
The next step is to decrypt the key:
# openssl rsa -in pulp3.apps.rdopenshift.si.wp.lan_exp2028.key -out pulp3.apps.rdopenshift.si.wp.lan_exp2028-decrypted.key
Now we can finally create the secret:
oc create secret generic pulp3-route-certs --from-file=certificate=../pulp3.apps.rdopenshift.si.wp.lan_exp2028.crt --from-file=key=../pulp3.apps.rdopenshift.si.wp.lan_exp2028-decrypted.key --from-file=caCertificate=pulp3.apps.rdopenshift.si.wp.lan_exp2028-ca.crt
secret/pulp3-route-certs created
And add the secret to the Pulp Operator Custom Resource yaml:
spec:
route_tls_secret: pulp3-route-certs
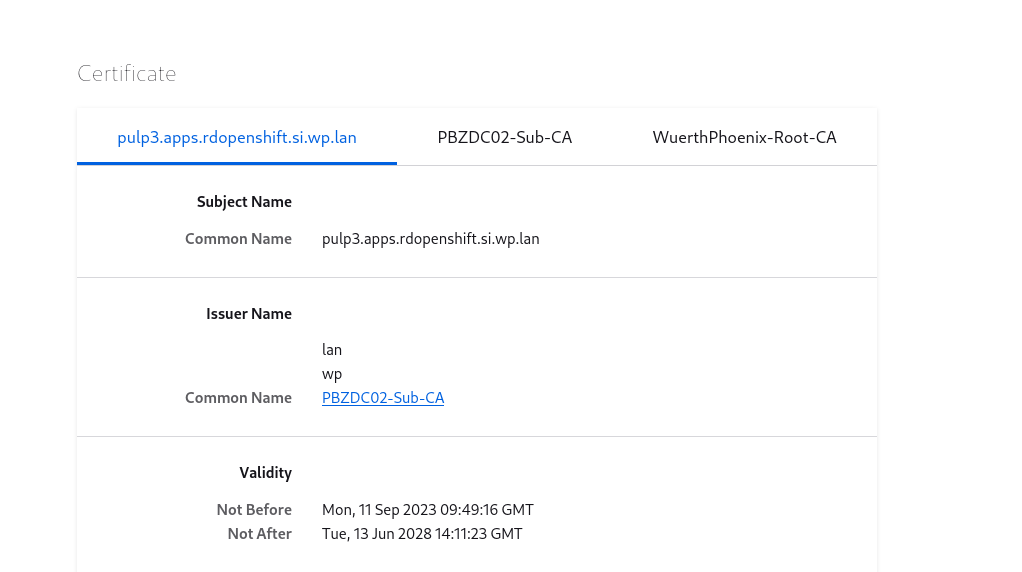
We can now verify that the Operator uses the correct certificates by checking the certificate exposed by the Operator route:
These Solutions are Engineered by Humans
Did you read this article because you’re knowledgeable about networking? Do you have the skills necessary to manage networks? We’re currently hiring for roles like this as well as other roles here at Würth Phoenix.






