Identify and Monitor Active Directory Domain Controllers with NetEye 4
NetEye 4, thanks to the Director module, offers very powerful mechanisms when it comes to fetching data from external data sources.
Among the external resources that can be configured in NetEye 4 there is clearly LDAP / Active Directory. This type of resource can be used for multiple purposes:
- Authentication of users
- Import of LDAP groups
- Import of hosts and many others object type
- Importing users for notifications
In this blog post let’s consider a scenario in which the agents have already been installed through the Self Service API, the hosts already exist in Director, and we want to identify the domain controllers, integrate some Custom Variables, apply a specific host group, and then apply a Service Set dedicated for monitoring DNS, LDAP and NTP services.
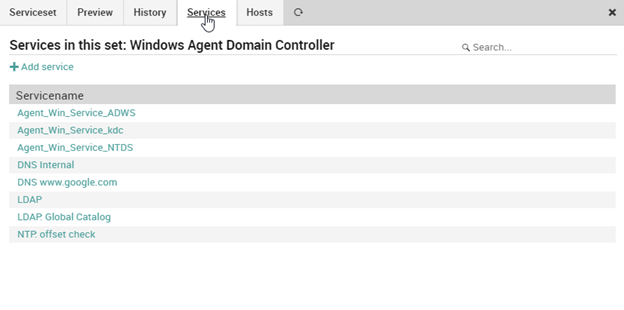
The Service Set can be downloaded from our github repository and imported using Director’s Basket feature. Next you need to adapt the LDAP and LDAP: Global Catalog service templates.
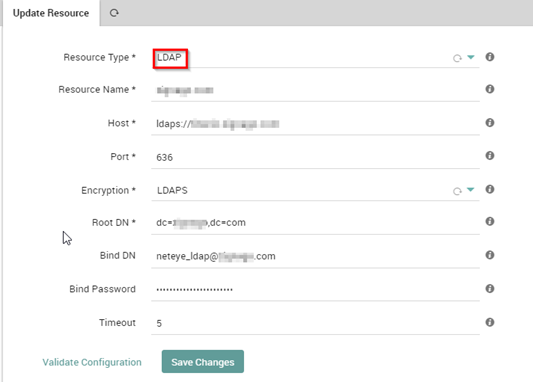
LDAP Resource Creation
In order to use the data made available from an Active Directory or LDAP source, you must first create an LDAP-type resource from the Configuration > Application > Resources menu.
Remember the importance of using an LDAPS connection.
After creating the resource we can use the automation functionality of the Director module to import the data of interest from the domain controllers and synchronize them with existing data.
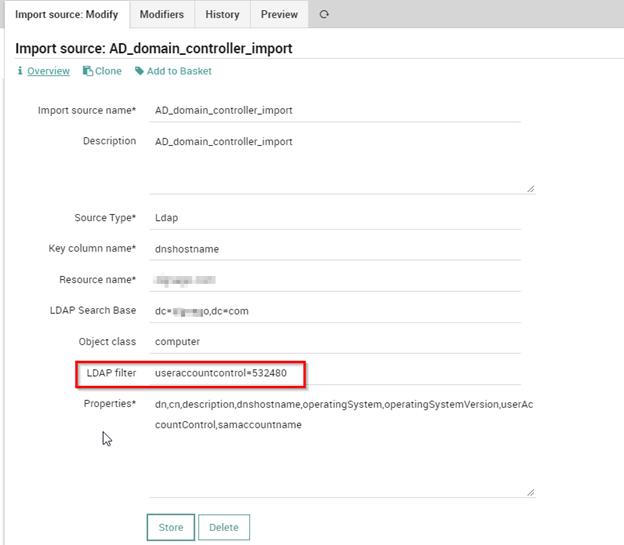
Import Source Creation
Using an Import Source, we can use our previously created resource to identify domain controller type computers very easily: it’s sufficient to use a filter on the UserAccountControl field with the value 532480.
In the properties field it is necessary to fill in a comma-separated list of LDAP properties that should be fetched. In our example we want: dn,cn,description,dnshostname,operatingSystem,operatingSystemVersion,userAccountControl,samaccountname.
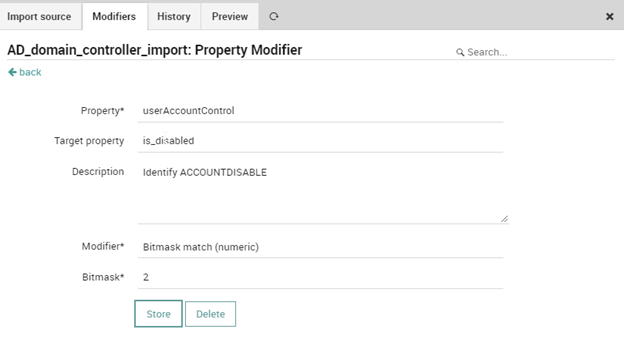
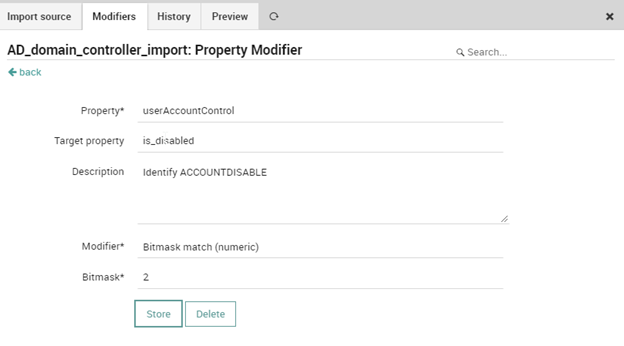
Subsequently, thanks to the Modifiers, we can verify the properness of the data obtained from the previous query in two steps:
- It’s possible to check and subsequently exclude any disabled hosts by creating an ad_hoc property called is_disabled which, thanks to a control (bitmask match with value 2) on the UserAccountControl field, will be defined as true or false.
- We can then use the is_disabled field to perform a blacklist based on this field whenever the value is true.
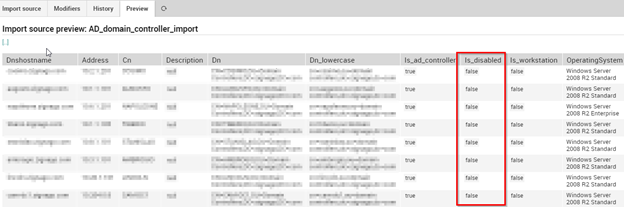
Finally, we can check the result shown in the Preview tab.
Sync Rule Creation
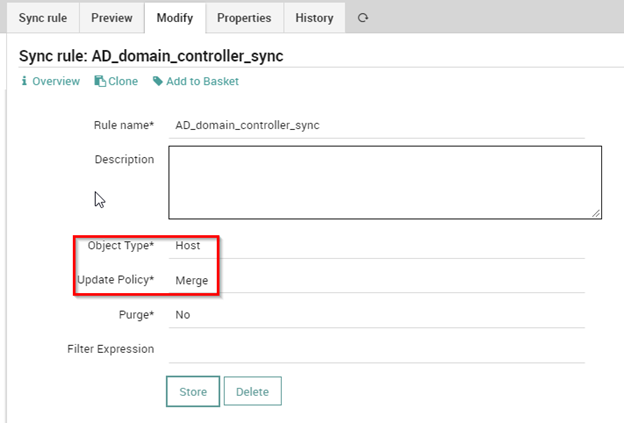
Using a Sync Rule, we can use the data prepared during the Import phase with the aim of merging existing data relating to domain controllers type hosts.
The Sync Rule must thus be created with “Object Type” Host and “Update Policy” Merge.
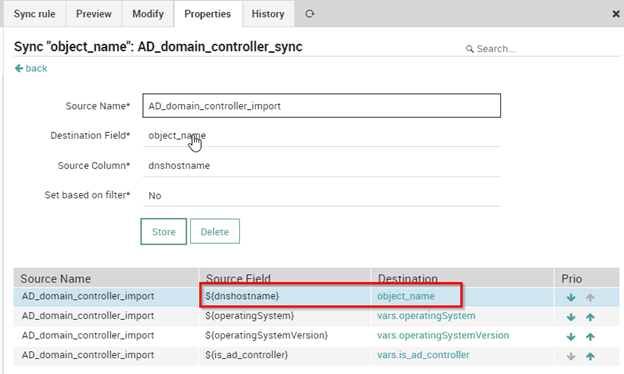
In the properties we must uniquely identify the host domain controllers using the dnshostname field associating it with the target field object_name.
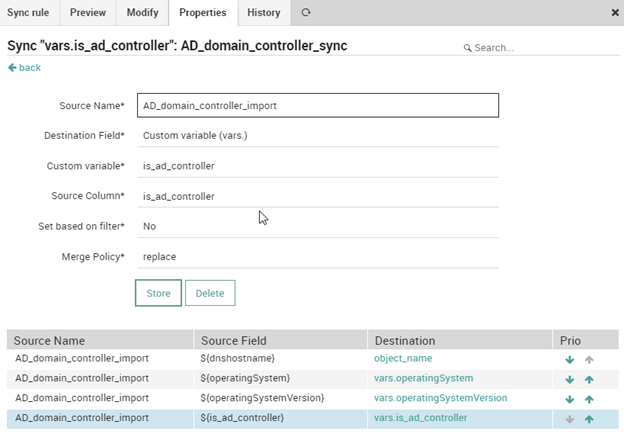
We can also enhance some Custom Variables to track the name and version of the operating system and a field of the boolean is_ad_controller type to identify domain controllers:
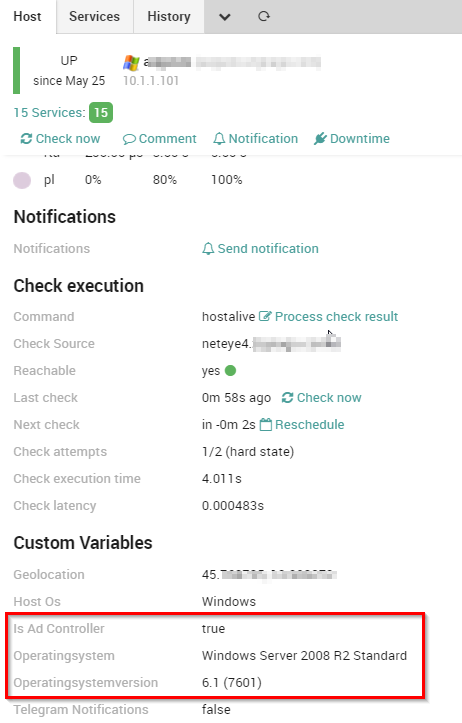
This is the result after importing the data:
Host Group and Service Set Association
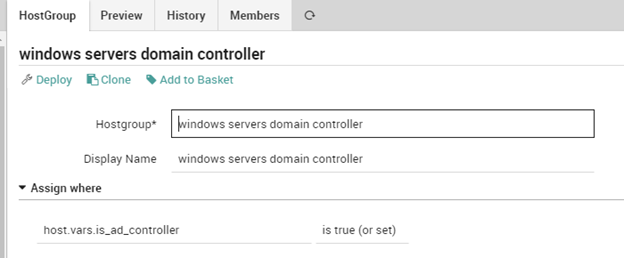
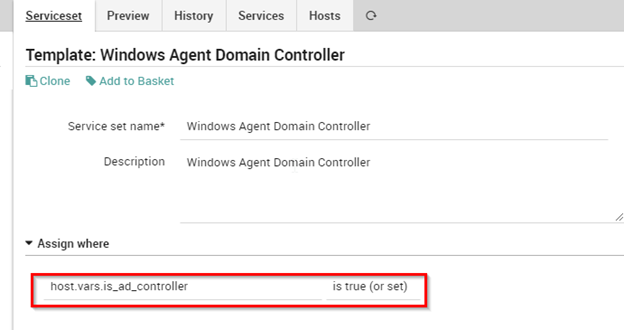
Now that we have the information, we can easily create a Host Group dedicated to Domain Controllers using an Assign where rule on the field of type boolean is_ad_controller and apply the imported Service Set in the same way.
HostGroup
ServiceSet
In conclusion we will end up having a dedicated Host Group that identifies only the domain controllers along with a series of specific controls just for these hosts, which clearly can be extended according to varying needs.
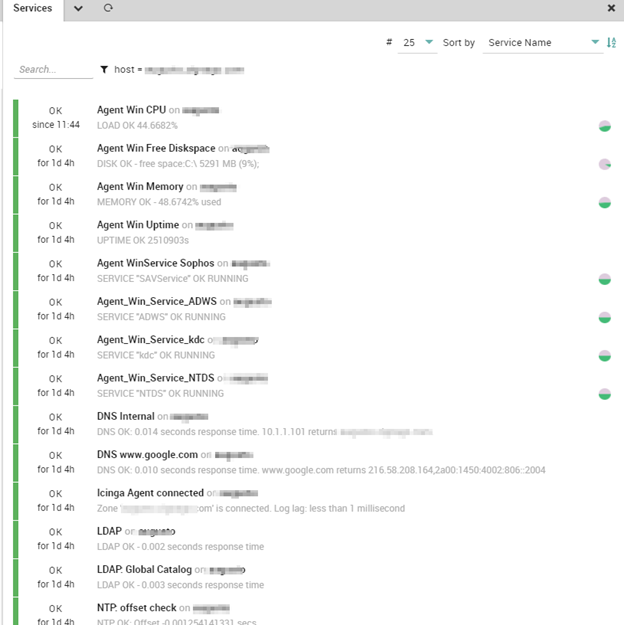
Below is an example of the controls applied to a domain controller host: