Log off an RDP User Session through the NetEye Command Orchestrator Part 2
In our previous post we discussed how to handle RD users using CMDO, focusing on the scripts needed to obtain a unique identifier for each users in the RD Farm. In this post I want to focus on how to create the CMDO commands and set their permissions correctly.
Our user case
As an admin I want to let NetEye users handle RD Sessions autonomously, but at the same time I don’t want them to connect directly to those servers. Only certain users need access to this command.
Using CMDO
Please refer to this link for more information about the commands discussed: https://neteye.guide/4.22/service-management/IT-operations.html
1. Creating a command group
In order to filter those who can execute the RD command, we’ll create a command group as follows:
icingacli cmdorchestrator commandgroup create \
--name 'RD Commands' \
--description 'commands to list and kill RD hanged sessions'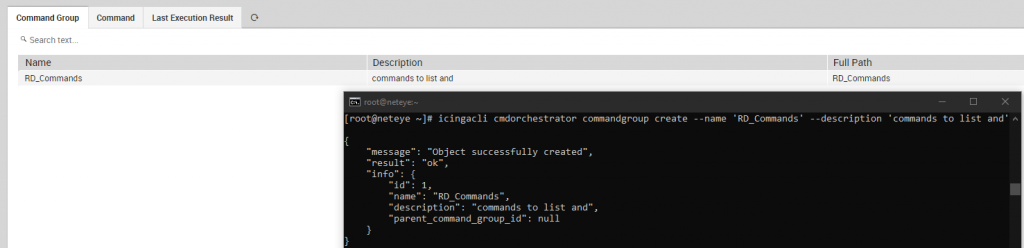
2. Creating commands
We’ll create 2 commands, one will get a list of all hanged user sessions with their IDs meanwhile the other will let you kill a session using those IDs.
Please note that we have to escape json-array elements with double quote backslash, sometimes even 4 of them as in these examples.
icingacli cmdorchestrator command create \
--name Kill_RD_Session \
--command-type remote \
--command "C:\\\\Windows\\\\System32\\\\WindowsPowerShell\\\\v1.0\\\\powershell.exe" \
--command-parameters '["-File", "C:\\\\ProgramData\\\\icinga2\\\\etc\\\\icinga2\\\\scripts\\\\Disconnect_RDPSessions.ps1", "-RDPID", "$RDP_SessionID$"]' \
--monitoring-object-filter 'host_name=RDBroker.lab' \
--command-group-id 1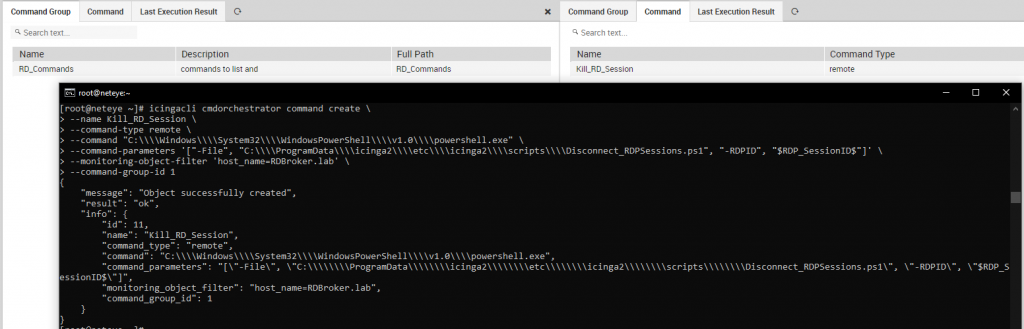
icingacli cmdorchestrator command create \
--name Check_RD_Sessions \
--command-type remote \
--command "C:\\\\Windows\\\\System32\\\\WindowsPowerShell\\\\v1.0\\\\powershell.exe" \
--command-parameters '["-File", "C:\\\\ProgramData\\\\icinga2\\\\etc\\\\icinga2\\\\scripts\\\\Check_RDPDisconnectedSessions.ps1"]' \
--monitoring-object-filter 'host_name=RDBroker.lab' \
--command-group-id 1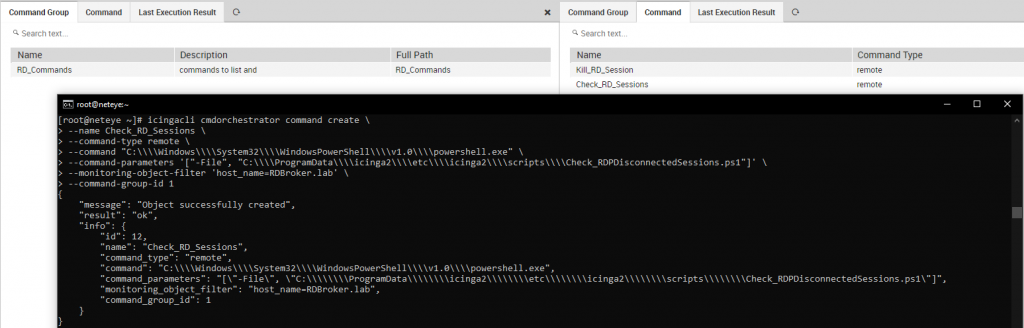
3. Creating commands
As we already mentioned in the previous post, we’ll use an integer variable as a parameter. We’ll have to add it to our Kill_RD_Session command
#Get the command id
icingacli cmdorchestrator command list
#Add the variable
icingacli cmdorchestrator commandparameter create \
--command-id '11' \
--parameter '$RDP_SessionID$' \
--parameter-type 'number'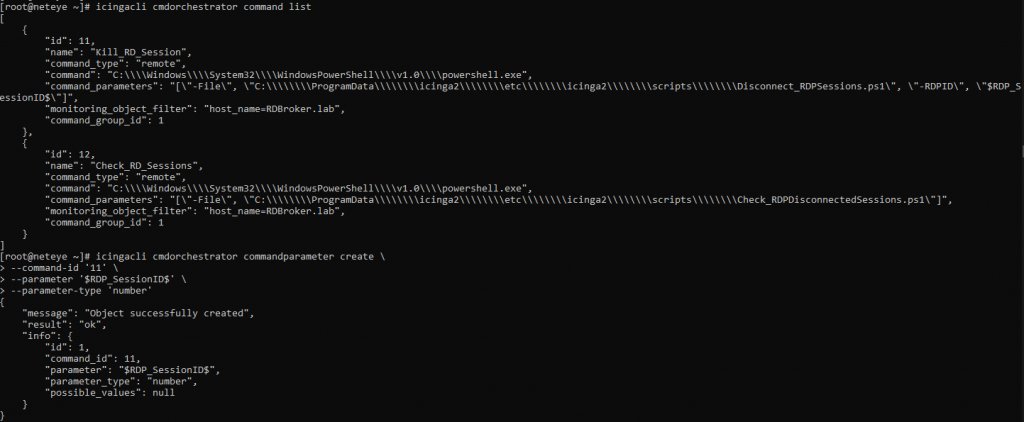
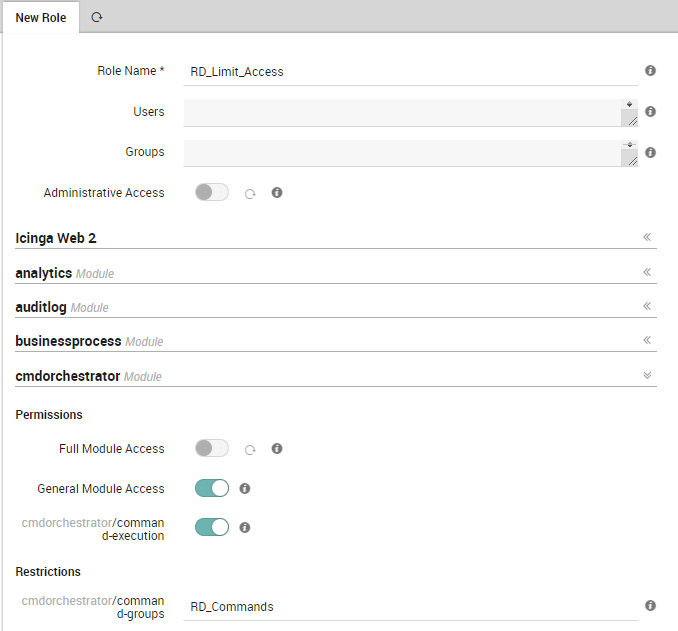
4. Limit access to Command Group
We want to limit access to these commands to only certain NetEye users. In order to do so we need to change the role configuration as shown below.
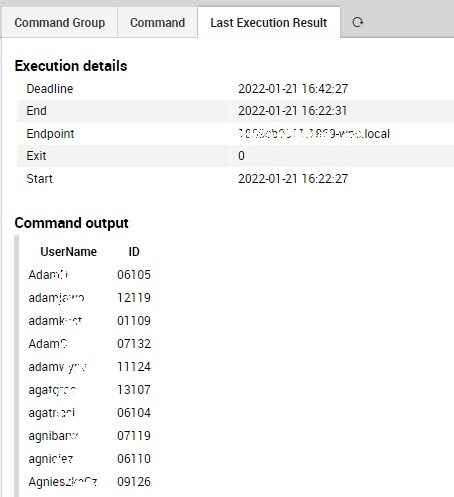
Now our CMDO solution is complete and ready to handle sessions in our RD Farm. If there are hanged sessions you should get an output like this on CMDO.
These Solutions are Engineered by Humans
Did you find this article interesting? Does it match your skillset? Our customers often present us with problems that need customized solutions. In fact, we’re currently hiring for roles just like this and others here at Würth Phoenix.






