In the last few weeks I installed and configured some nBoxes with the new ntopng version 5.2. Now I’d like to briefly tell you all about it.
For all of you who don’t know what an nBox is, I’ll relay the official definition here:
nBox Recorder is a network traffic disk recorder application. With nBox Recorder you can capture full-sized network packets at gigabit rate from a live network interface and write them into files or analyze them with the ntopng tool.
After we’ve put the nBox into the network and forwarded the network traffic from a mirrored port on the switch to a network port on the nBox, you can already begin to see the first data in the ntopng interface.
I’m currently changing this configuration and collecting the mirrored data via the nprobe daemon which I start on this port, and forwarding the processed data to the ntopng. The reason for this is to avoid possible future bottlenecks and allow the forwarding of this data to other ntopng installations.
I then activate the ntopng daemon so that it reads the data via the nprobe and writes it to the new ClickHouse database.
From ntopng release 5.2 onwards you can use a ClickHouse database instead of nindex, as this database is a high-performance SQL database that’s much faster than nindex. You can find the official ClickHouse documentation here.
The switch to using the ClickHouse database is the main innovation for the new ntopng 5.2 version.
ntopng integrates with ClickHouse to store historical flows and alerts. If ClickHouse is not pre-installed, you can easily install it by following the official installation guide on the ntop site. Using this database also enables detailed raw traffic analysis in ntopng.
Following the “Historical flows” view for flow analysis by application, which you can do by enabling the ClickHouse database, points “1” and “2” show how to search for applications in the period selected at the top.
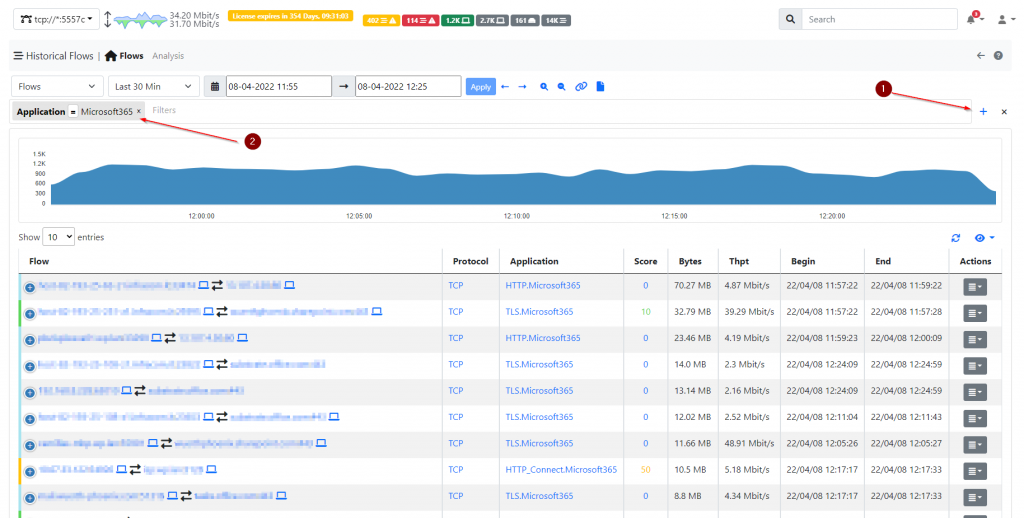
It’s precisely this new “Historical Flows” view that I find particularly special and intuitive. It gives you a simple analysis of traffic peaks up to the layer 7 level.
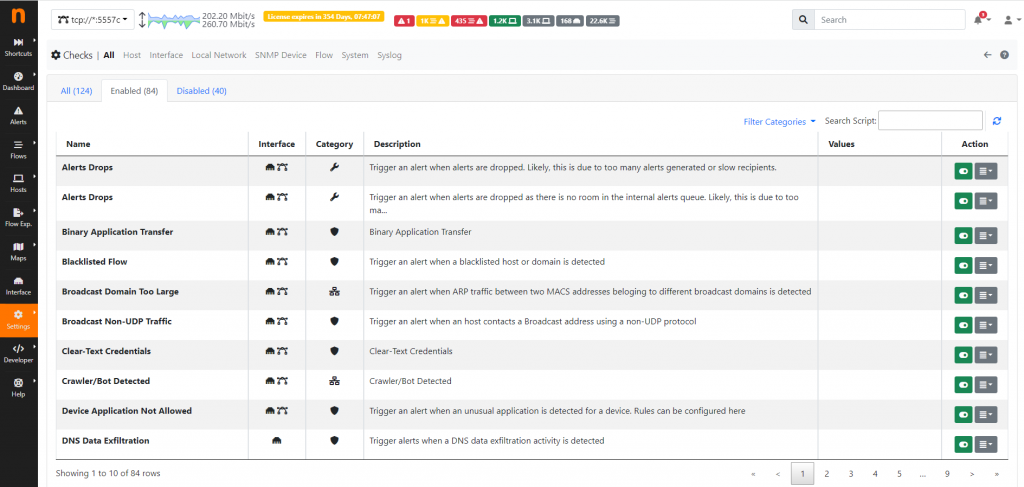
Another very successful implementation is the predefined alarms, which can offer an initial level of support in the event of any cyber attacks. You can send these alarms to various environments via mail, syslog, webhook, etc.
Here’s a screenshot of the alerting overview:
Conclusion
The current nboxes are easy to install and if you have them properly pre-installed, they will work right out of the box. With just a few configuration steps, you can have a top network analysis and alarm system in just a few hours.
These Solutions are Engineered by Humans
Did you find this article interesting? Does it match your skill set? Our customers often present us with problems that need customized solutions. In fact, we’re currently hiring for roles just like this and others here at Würth Phoenix.







