This article explains how the Cyber Threat Intelligence platform SATAYO serves as a powerful resource to optimize processes and strengthen threat coverage within the Würth Phoenix Attacker Centric SOC. We will analyze the utilization of SATAYO’s internal resources for creating Detection Rules and managing SOC alerts. Additionally, we will examine how the logs in SIEM can mutually contribute to improving the quality of the elements retrieved through SATAYO.
SATAYO and Detection Rule Summary
Before we start, it’s essential to provide a brief explanation of SATAYO for those of you who are not familiar with it. SATAYO is a software that integrates a variety of different tools, and thus numerous sources, with the aim of providing an overview of a specific organization from an external point of view, highlighting its vulnerabilities and the potential attack vectors that can be exploited by cyber criminals.
For more details, see the official documentation available here.
The elements I want you to understand today are the Detection Rules. These rules simply apply logical conditions to all logs passing through SIEM. If a log meets these logical conditions, a security alert is then triggered.
Custom Detection Rule
Once we understand how SATAYO works and is used, we can proceed by investigating how to create detection rules that integrate its items.
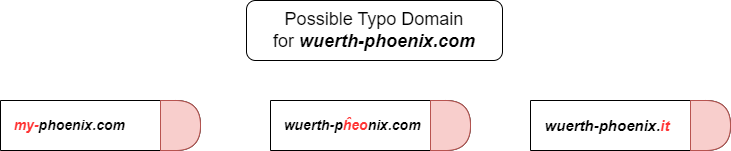
Suppose we want to construct rules to analyze SMTP traffic, aiming to intercept direct e-mails or those coming from domains similar to the company’s official one. In our case, let’s take wuerth-phoenix.com as an example.
Phishing campaigns and typosquatting/URL hijacking attempts typically use domains similar to official ones. The definition of “similar” can take various shapes; for instance, they can include the company name in full or in part, such as my-phoenix.com. They may have characters arranged in a different order or similar characters, such as wuerth-pĥeonix.com. Trivially, they may also differ by TLD, as in the case of wuerth-phoenix.it. These are only a few examples and do not cover all possible forms used in these attack techniques.
An effective solution for creating detection rules could be the use of so-called fuzzy queries. In this way we can consider all possible permutations of two or more characters within a given keyword. However, this approach could generate alerts even for legitimate domains; since it also includes cases where the number of permutations of characters is zero.
In order to solve this problem, exceptions must be added for official domains. One possible solution would be to create a list of known official domains. However, this list could become out-of-date if it’s not updated periodically. In a similar way, adding exceptions each time alerts are generated would be time-consuming and might not cover all cases.
In this context, SATAYO comes into play, providing a periodically updated list containing both new domains registered by the company and similar domains detected. This would potentially allow us to construct detection rules without the use of fuzzy queries, relying only on those domains that actually exist.
The same logic can be extended (and not limited) to SMTP traffic, as connections or requests for connections to such domains can also be monitored, thus extending coverage over potential new threats.
Powered SOC Analysis
Furthermore, as you should already know, SATAYO does not limit itself to the analysis of domains, but also includes a section dedicated to data breach victim accounts. In addition to compromised e-mail addresses, this section provides detailed information on the data breach. For instance, it provides dates of compromise, dates of publication, and types of compromised information, such as first names, last names, emails, passwords, social media profiles, etc.
SOC analysts receive this information and can use it to manage alerts relating to, for example, brute force attacks. This approach raises the level of analysis, allowing more precise details to be provided and improving the quality and quantity of information reported. The availability of details on past compromises allows analysts to more effectively mitigate potential threats, thus helping to strengthen the organization’s overall security.
Mutual Benefit
To conclude, the relationship between SATAYO and the SOC world is two-sided. It’s not just the former that provides valuable information and resources to the second, but also vice versa. In the same way, SATAYO can use the data contained within SIEM to improve the quality of its own analyses, promoting mutual and continuous improvement. This synergy between the two platforms allows for a dynamic collaboration, in which information flows in both directions, enhancing the overall effectiveness of information security systems.
These Solutions are Engineered by Humans
Did you learn from this article? Perhaps you’re already familiar with some of the techniques above? If you find cybersecurity issues interesting, maybe you could start in a cybersecurity or similar position here at Würth Phoenix.






