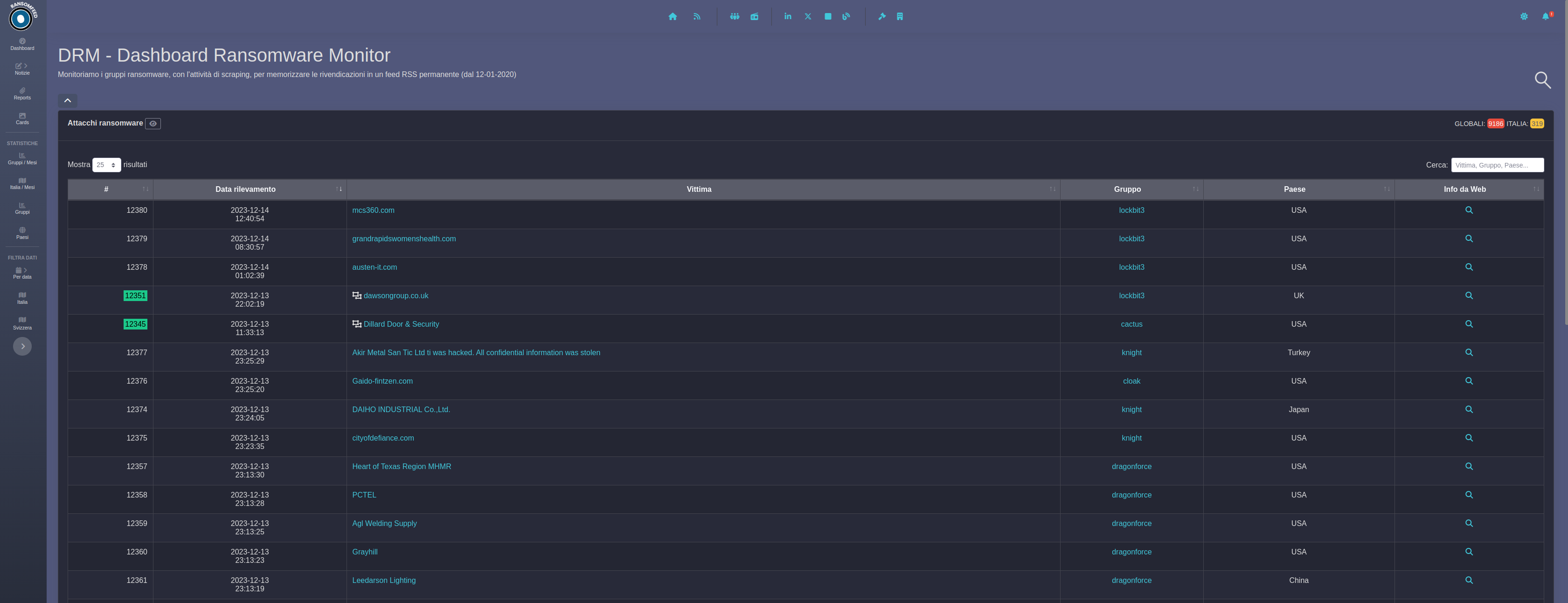
Ransomware Double Extortion Attack: 2025 Overview

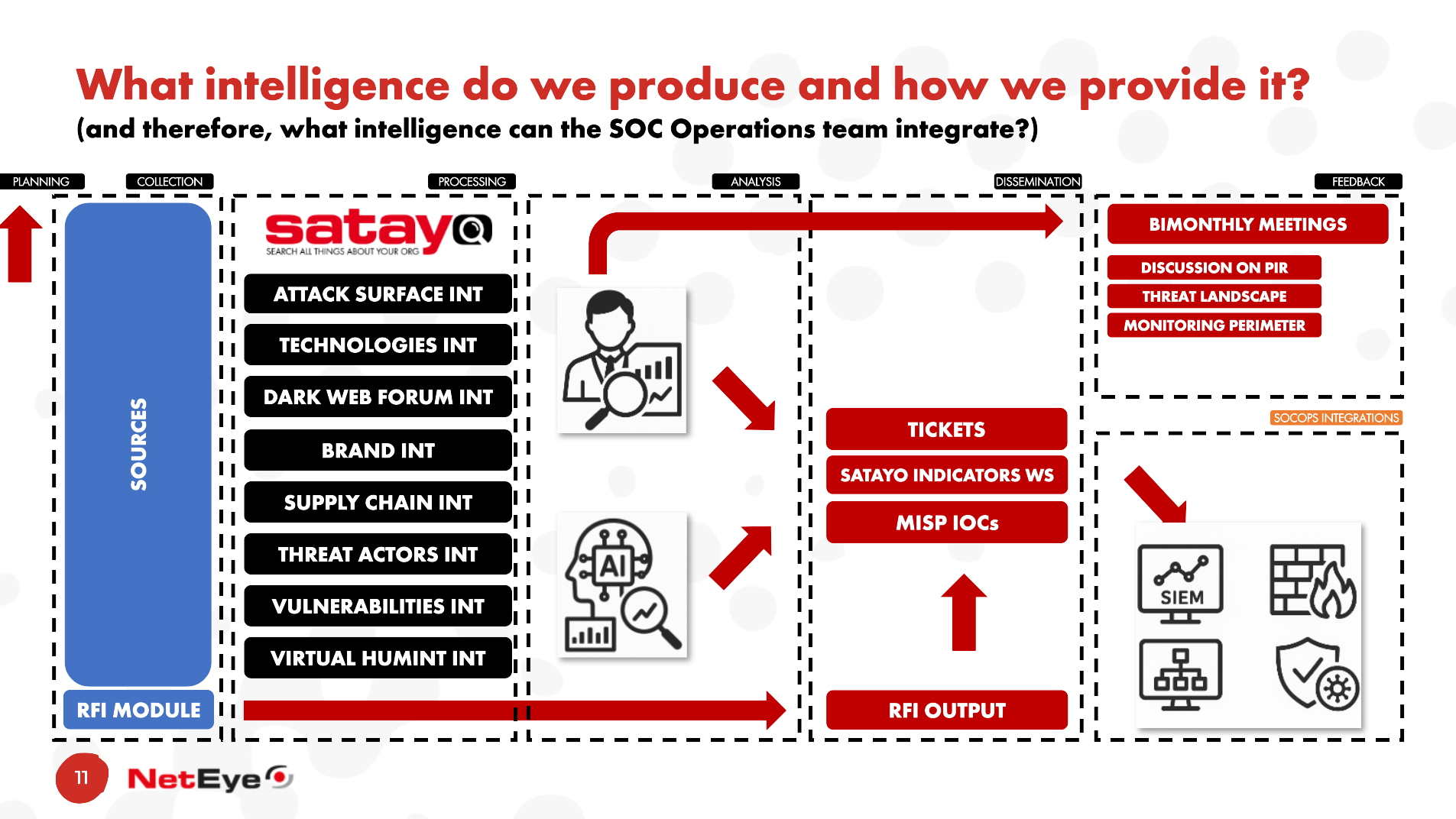
As 2025 comes to a close, we can make some observations regarding the evolution of the double-extortion ransomware attack landscape. The data shown is the result of the enrichment performed within SATAYO starting from the data made available by the Ransomfeed project. The URLs of the Data Leak Sites (DLS) of the various ransomware gangs…
Read More